It is repeated so much, the user is often the fragile piece , it is often him responsible for his own piracy.
It is usually once hacked that he becomes aware of it and is sometimes wary at times unjustly of everything.
To make the most of millions of services on the Internet in a secure way, you need to acquire basic knowledge about hacking, ie computer security.
These are unfortunately not taught, so here is an article to help you see clearly.
We'll see how to secure your Facebook account by keeping a keen eye on your data.
Before posting anything
Although it's probably already too late and you have published a lot of personal information about yourself, know in the future that even if you delete or hide your content, it is always saved somewhere.
It's like when you talk to someone, you can always say that you lied, but the information was shared you can not "decide".
Also note that your email addresses and other photos can be saved by anyone with access to them.
What we do not tell you
Facebook uses "robots" that "read" and automatically analyze your private messages .
That's why you have the right to very targeted advertising.
And it's also by looking at advertisements at your friends that you can even guess what most of their private messages are about.
You can even guess the sites they are used to frequent because Facebook also uses tracking pixels . I quote :
We use tracking pixels to personalize your usage and analyze how people use products and services. For example, we can use tracking pixels to see if someone who has used a specific browser has posted an ad on Facebook and has also purchased a product from that advertiser.
So you thought you were already being spied on everywhere, but this is really pushed to the limit of privacy.
Besides you can test yourself, say hacking for example to your friends on Facebook and you will see corresponding ads the following week.
Security through darkness
This term is often used to define the fact of hiding information that one does not want to show instead of deleting it.
Facebook offers the possibility to choose who sees your content, so take a good half hour to check your settings.
To do this click on the icon with the small padlock at the top right and then refine your parameters according to the available choices.
You can also find these options by clicking on the icon with the small gear then Privacy .
Generally, the setting you can leave Public is for people who can contact you unless you want to book your account only with your current friends.
The other settings depend on what you want to display to specific people , so set them as you see fit. Just know that you do not necessarily need to post everything to someone you do not know for example in real life .
In the confidentiality part always, I draw your attention on the part called " Who can find me with a search? "
Two settings are available, the first concerns the search for your information and the second the indexing of your profile by the search engines.
If you allow these settings, a user who knows your email address will be able to find your Facebook profile. In the second case, he will be able to find your profile via a search engine.
Secure your Facebook account with dedicated tools
I am not particularly fond of this option, but some applications allow you to secure your account / your privacy or that of your children.
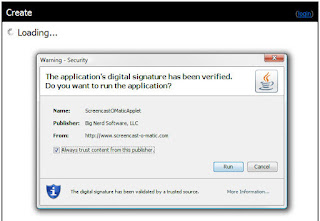
To use it, simply log in with your Facebook account and authorize the application.
You will then have the choice to secure your account or that of your children:
Securing your Facebook account effectively
Once you understand the information you post and post, you can also secure your account against hackers.
And if you had been hacked in the past, there is a good chance that the settings that will follow have not been applied.
Let's go to the security part of Facebook.
Enable Secure Browsing , this will prevent a user from recovering your password on the fly across the network using the https protocol.
Enable Notifications when logging in at least by email address to indicate any unusual successful login.
You can enable Connection Approvals if you want to prevent the connection from an unknown browser by first requesting a code that you will receive via SMS. The previous setting indicates an unusual connection but does not prevent it, whereas here it will enter the code received by SMS.
The Code Generator allows you to override SMS sending with codes for sign-in approvals.
You can add Trusted Contacts if this includes someone in your family. Do not add anyone. In case of loss of your account, Facebook will go through this contact to regain access to your account.
The known devices are the devices where "you" you are connected. Facebook, for example, retains connection information to make navigation more enjoyable. Check that the devices belong to you and that you have connected well with them.
Last but not least, Active Sessions . You should check these sessions regularly for locations and devices that are allowed to connect. The level of security is lowered for these devices because Facebook imagine that they are yours. If that's the case, if it is not someone can currently be logged into your account. Attention by cons instead of connection often wrong. I am told, for example, that the place of my current session is Paris while I live at 500km.
In addition, if you are used to logging into your Facebook account using a smartphone in EDGE connection, 3G ... etc or through a hotspot, you will have IP addresses from different places . This is because your 3G / 4G mobile connection becomes a normal Internet connection and that via the IP addresses of your ISPs.
So you have to know how to distinguish between an IP address from a hacker, or from your own ISP. And that's not easy, you can try sites like ip-adress.com to view details about IP addresses.
Only all manufacturers do not communicate their IP ranges and it is therefore difficult to know if the IP address comes from a hacker at a given ISP or if it is only an IP address used by your mobile.
Conclusion
We've seen how to secure your Facebook account with basic settings that everyone should be aware of.
Unfortunately I still get too many calls for help when the damage is already done. So I hope this article will help many of you.
And finally, for the most skeptical, there are free services to secure his facebook account "automatically" by repeating what I talked about, and more.
Secure.me of avast! is a "real-time anti-virus" for your account.
And privacyfix allows you to set a ton of settings for even more site than Facebook, I recommend it.
You can also take the How to Protect Your Computer and Privacy course to get a whole bunch of techniques to stay protected effectively.
You can also take a look at my article How a hacker can hack a facebook account for further practice.